Top 10 ReliaQuest Competitors Worth Evaluating in 2026

.avif)
.avif)
ReliaQuest built its reputation on a practical idea: keep your existing security tools, connect them through GreyMatter, and get unified visibility without ripping anything out. For many enterprise teams, that overlay model was the right call. It preserved existing investments and gave leadership a single operational layer across a fragmented stack. So why are security leaders evaluating ReliaQuest competitors?
The reasons vary. In some environments, teams feel that deeper detection tuning still depends heavily on ReliaQuest’s team, and custom rule changes may move more slowly than they expected from pre‑sales conversations.
In others, analysts notice recurring alerts in the console that they assumed the service would have learned to suppress over time. For some security leaders, the overlay architecture no longer lines up cleanly with how their infrastructure and security operating model have evolved.
None of those tradeoffs is a judgment on ReliaQuest. It's a description of what the overlay model does and doesn't do well. If those tradeoffs don't fit where your environment is heading, it makes sense to understand what else is available.
This guide covers ten alternatives across different MDR architectures. For each, we cover what the service does, where it fits, and where it falls short.
TL;DR:
- The MDR market has split into three categories: Legacy MDR, AI SOC, and AI MDR. Each carries a fundamentally different accountability model, and confusing them leads to mismatched procurement decisions.
- ReliaQuest's overlay model is structurally additive, not substitutive. GreyMatter adds a layer on top of existing SIEM and EDR spend, and detection customization remains locked behind ReliaQuest's team.
- Investigation depth per integration matters more than integration count. A provider that covers most alert types for your critical tools will often outperform one with broad integration coverage that ingests only a narrow set of alert types per tool.
- AI MDR is where current market demands are heading, but capabilities vary significantly across providers. Contractual accountability, investigation transparency, and response authority are the dimensions that separate marketing claims from operational reality.
Key Pain Points Driving Buyers to ReliaQuest Competitors
The most common complaints in ReliaQuest evaluations cluster around three areas.
First, detection customization is locked behind ReliaQuest's team. Custom detection delivery is often slower than represented in pre-sales, which means your coverage gaps persist until the queue clears.
Second, alerts that should be resolved silently still surface in the console without learning from prior resolutions. That points to a deeper architectural issue: without structured context that captures why a verdict was reached and what "normal" looks like for your environment, the platform keeps re-triaging what it should already know. This is the alert fatigue problem in its most expensive form.
Third, onboarding and integration complexity hits lean teams hard. Managing the overlay alongside existing tools creates operational friction: alerting levels that need recalibration, events that should have been remediated silently, and response time concerns that compound over time.
The overlay model's core tradeoff is that it adds a layer without replacing anything. If that layer doesn't reduce your team's operational burden in practice, the additive cost becomes hard to defend.
Evaluation Framework for ReliaQuest Competitors
Before comparing individual providers, establish the dimensions that matter for your environment. These seven focus areas separate vendors who have thought through the operational reality from vendors who have thought through the pitch.
- Coverage breadth: Does the provider cover your actual stack (endpoint, cloud, identity, SaaS, and email) or only a subset? Get specific: which tools, which alert types, and how deep does the coverage go?
- Integration depth and directionality: How many alert types per tool are actually investigated? Read-only versus bi-directional? The gap between "we integrate with Wiz Defend" and "we investigate 90% of Wiz Defend alert types" is where real coverage differences hide.
- Investigation scope: Does the provider investigate every alert to resolution, or handle lower-complexity cases and hand back the rest? Escalation volume is the clearest signal.
- Response authority: What can the provider do autonomously versus what requires your approval? Pre-authorized containment is meaningfully different from a notification that something looks suspicious.
- Transparency: Can you see how investigation decisions were made: data used, logic applied, conclusion reached? The difference between Glass Box and black box operations becomes most visible when you're reviewing a decision you want to understand or challenge.
- Expert caliber: Who is actually behind the service? What are their backgrounds? Are they senior enough to lead an incident response engagement, or are they working through escalation procedures?
- Investigation triggers: Does the provider only investigate alerts from your existing tools, or also investigate findings surfaced through proprietary rules on your log data? If your current tools have gaps, a provider that depends entirely on those tools for signal inherits the same gaps.
No single provider wins on every dimension. The goal is to know which ones matter most for your environment before you start the conversation.
Top ReliaQuest Competitors to Know in 2026
The following ten providers span the three architectures outlined above. The comparison table is a directional summary. The profiles below provide the context that matters.
1. Daylight Security (Managed Agentic Security Services / MASS)
If your primary frustration with ReliaQuest is that the overlay adds cost and complexity without reducing the investigation work that lands on your team, Daylight's architecture solves that specific problem.
Daylight is a managed service that takes ownership of investigation and response, with a defined accountability model and full transparency into how every verdict is reached.
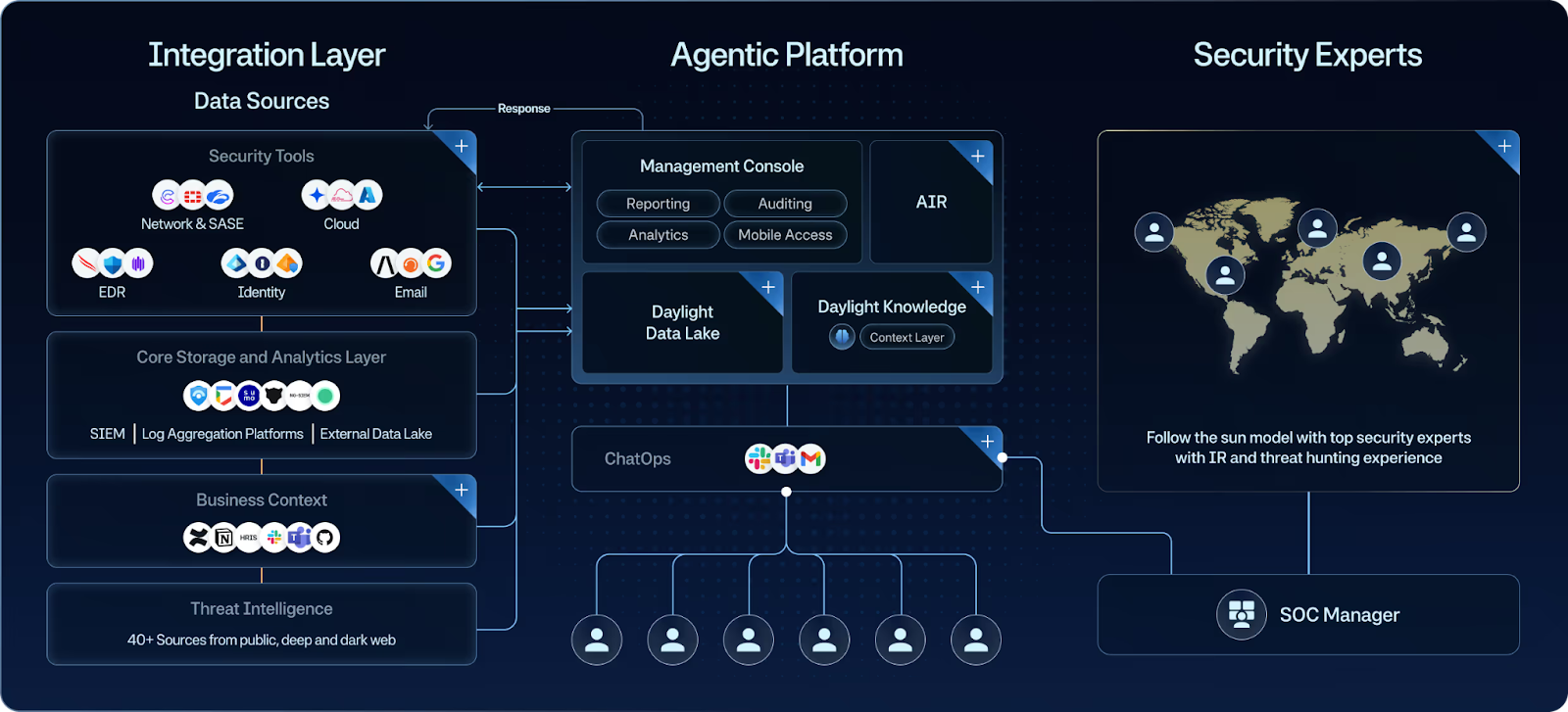
Daylight operates in a distinct category: Managed Agentic Security Services. AI agents investigate every alert with full context assembly, and security experts build the knowledge architecture that makes those investigations accurate and auditable.
The architecture addresses the three pain points that surface most often in ReliaQuest evaluations. Waiting on detection customization queues becomes a non-issue when Daylight runs proprietary detection rules directly on your log data, generating a second stream of investigation triggers that doesn't depend on your tools' alert coverage.
Alerts resurfacing without learning from prior resolutions get solved by bi-directional integrations that write back to close resolved issues at the source, so your dashboards reflect accurate status rather than accumulating stale open items.
And investigation opacity gets replaced by what Daylight calls Glass Box transparency: every decision is visible and auditable, showing what was checked, what data was used, what conclusion was reached, and why.
Key features
- Daylight Knowledge is a customer-specific context repository that builds continuously. Every investigation assembles three types of context in real time: telemetry, organizational, and historical. Investigations that appear ambiguous with incomplete context tend to become deterministic when full context is available.
- Two investigation triggers extend coverage beyond what your existing tools surface. Proprietary detection rules on log data generate a second stream of investigation triggers independent of the alerts your tools produce.
- Deep, bi-directional integrations cover the majority of alert types per tool. Bi-directional write-back closes resolved alerts at the source, so teams carrying backlog find that backlog addressed, not just triaged.
- Security experts with incident response and threat hunting backgrounds help with context building and scaling, low-confidence verdict review, and incident response leadership.
Best for: Mid-market to enterprise organizations with significant cloud environments. Best fit for mid-market to enterprise organizations with significant cloud environments, particularly teams replacing an overlay model who want managed investigation depth, contractual accountability, and a real reduction in re-triage volume.
2. CrowdStrike Falcon Complete (with Charlotte AI)
Falcon Complete is a managed detection and response service built directly on the Falcon platform. It extends CrowdStrike’s endpoint, identity, and cloud protections with 24/7 monitoring, investigation, and remediation handled by CrowdStrike analysts.
The service is engineered to maximize the value of Falcon telemetry, so the depth of investigation and response quality scale with the breadth of Falcon's deployment in your environment. Signals that originate outside the Falcon ecosystem can be incorporated, but this is not a cross‑stack correlation layer for a highly heterogeneous toolset.
Best for: Organizations standardized on CrowdStrike that want MDR tightly integrated with their EDR/XDR stack.
3. Arctic Wolf MDR
Arctic Wolf’s core differentiator is its Concierge Security Team: named experts who act as an extension of your internal staff. The MDR service is delivered through Arctic Wolf’s own platform and agent, which customers have come to rely on as their primary detection and response layer. If you already rely heavily on an internal SIEM, clarify how the two will coexist and what direct data access you’ll retain.
Before signing, it is worth getting very specific on what’s included in the base MDR service versus add‑ons or bundles. Cloud sources, identity coverage, and log retention are common areas where scope assumptions differ between buyers and vendors.
Best for: Organizations that value a relationship-driven model with a named team and want broad log coverage, primarily on-premises or hybrid.
4. eSentire MDR (Atlas)
eSentire operates on the Atlas Security Operations Platform with a contractual Mean Time to Contain of 15 minutes across all tiers. The platform claims 300+ integrations. The Microsoft alignment is meaningful: eSentire offers a dedicated Sentinel service, operating Sentinel alongside Atlas.
The MSSP heritage is worth examining. The operating model has evolved, but verify investigation depth versus alert forwarding for your specific tool stack. Integration breadth does not automatically translate to investigation depth. With 300+ integrations, confirm that cases land with the right response authority and don't create a routing overhead problem in place of an alert fatigue problem.
Best for: Enterprise environments with heterogeneous stacks and substantial Microsoft investment.
5. Sophos MDR
Sophos MDR operates across two tiers. Essentials provides 24/7 monitoring and containment guidance. Complete adds full-scale incident response. Sophos reports 26,000+ MDR customers across seven global SOCs.
Investigation depth for non-Sophos telemetry sources is limited. If your stack spans multiple EDR platforms, identity providers, and SaaS tools, validate how deeply each source is actually investigated versus ingested.
Best for: Organizations wanting fast, predictable MDR, strongest in Sophos or predominantly Microsoft environments.
6. Intezer
Intezer's "Forensic AI SOC" platform supports autonomous triage and investigation across endpoint, cloud, identity, network, and SIEM sources. Its AI-driven Detection Engineering is natively coupled with daily triage outcomes, so detections are continuously validated. This is a tool, not a managed service. The customer retains all accountability.
Best for: Teams with skilled operators who want AI-augmented triage at scale and are comfortable owning the operational burden.
7. Prophet Security
Prophet Security's Agentic AI SOC Analyst offers three configurable automation modes: fully automated resolution for low-risk alerts, expert-in-the-loop for medium-risk, and automatic escalation with full context for high-risk.
Three modules (SOC Analyst, Threat Hunter, and Detection Advisor) support natural-language interaction. Response decisions remain with the customer.
Best for: Organizations that want configurable automation levels with humans still in the loop for all decisions.
8. Dropzone AI
Dropzone AI positions its AI SOC analyst as being integrated with 85+ security tools, but you should verify which of your specific products are supported and at what depth.
One notable capability is its ability to automatically message impacted users to confirm activity details and clarify intent. The service is operated by your team rather than a managed provider, and it does not function as a traditional MDR with contractual response obligations.
Best for: Teams with high alert volume looking for AI-augmented triage.
9. Microsoft Sentinel + Defender XDR
Sentinel and Defender XDR are converging into a unified platform in the Defender portal. E5 license holders receive up to 5 MB of free data ingestion per user per day.
Microsoft Defender Experts for XDR is the managed service offering, but it is explicitly scoped to Microsoft Defender XDR services. Non-Microsoft signals ingested into Sentinel are not covered by the managed component.
Best for: Microsoft-heavy environments with internal SOC capacity to operate the platform.
10. Palo Alto Networks Cortex XDR (with Unit 42)
Palo Alto positions Cortex XDR as the detection and investigation layer for an AI‑driven SOC, with an option to expand into Cortex XSIAM for broader data and automation coverage. It ingests endpoint, network, and cloud telemetry to correlate events, surface incidents, and support guided investigations, with Unit 42 services able to work directly inside the same environment for hunting and incident response.
Best for: Palo Alto customers wanting native XDR with embedded managed services.
Choosing the Right ReliaQuest Alternative for Your Environment
The vendors in this guide that execute Legacy MDR well do so within the constraints of that architecture. If those constraints match your environment, they are reasonable choices. If they don't, a stronger execution of the same model won't resolve the underlying mismatch. Cloud, identity, and SaaS coverage gaps don't close because the connector layer has more integrations. Re-triage volume doesn't drop because the SOAR playbooks run faster.
The more precise question is where your environment is heading and which architecture is built for that trajectory. If your primary frustration is additive cost without workload reduction, the problem isn't which overlay to pick. It's whether the overlay model itself is the constraint. If your team is still re-triaging alerts the service should have resolved, the architecture is failing at the investigation layer, and swapping one Legacy MDR for another doesn't change that.
For teams that have hit the ceiling of the overlay approach, or that evaluated AI SOC tools and found the operational burden stayed with them, AI MDR is the category worth examining. Capabilities vary significantly across AI MDR providers, so the evaluation work still matters. But the starting point is the architecture, not the feature list.
Daylight solves the specific problems that drive ReliaQuest evaluations: investigation opacity, alert re-triage, signal gaps from single-source triggers, and the operational burden of managing an additive layer.
The Glass Box model means you can see exactly how every verdict was reached. Bi-directional integrations close resolved alerts at the source, so your dashboards stay clean. Two investigation triggers mean coverage extends beyond what your existing tools surface. And the service takes accountability for investigation and response outcomes, so the work actually leaves your team's plate.
If you're ready to see what investigation looks like when context drives every verdict, book a demo to see Daylight in action.
Frequently Asked Questions About ReliaQuest Competitors
Is Replacing ReliaQuest Mainly a Tooling Decision or an Operating Model Decision?
Usually both, but the operating model is the harder problem. The core question is whether you want another additive layer on top of your existing stack, a customer-operated AI SOC tool your team still has to run, or a managed service that takes on investigation and response with a clearer accountability model. The tooling follows from that choice.
What Should I Ask Any MDR Provider Before Switching from ReliaQuest?
Three questions that expose real operational fit. First: "For my specific tool stack, how many alert types per integration are investigated versus ingested?" Second: "Can you push containment actions directly into my environment, or does my team execute?" Third: "What investigation history, detection rules, and telemetry data can I export at contract termination?"
What Should Matter More Than A Long Integration List?
Investigation depth, transparency, and whether alerts actually get resolved without boomeranging back to your team. A long integration list sounds good in procurement, but it matters less than how many alert types are truly investigated, whether the provider can act in your environment, and whether you can see why a verdict was reached.
What is the Practical Difference Between AI Soc and AI MDR in a ReliaQuest comparison?
AI SOC is a tool category. It automates Tier 1 triage, but your team operates it and owns the outcome. AI MDR is a managed service category. The provider operates it, and accountability, transparency, and response authority become the real evaluation questions.
If you are leaving an overlay because your team is already overloaded, that distinction matters more than feature density.





