A Compromised AI Library and an Expanding Supply Chain Campaign
.avif)
.avif)
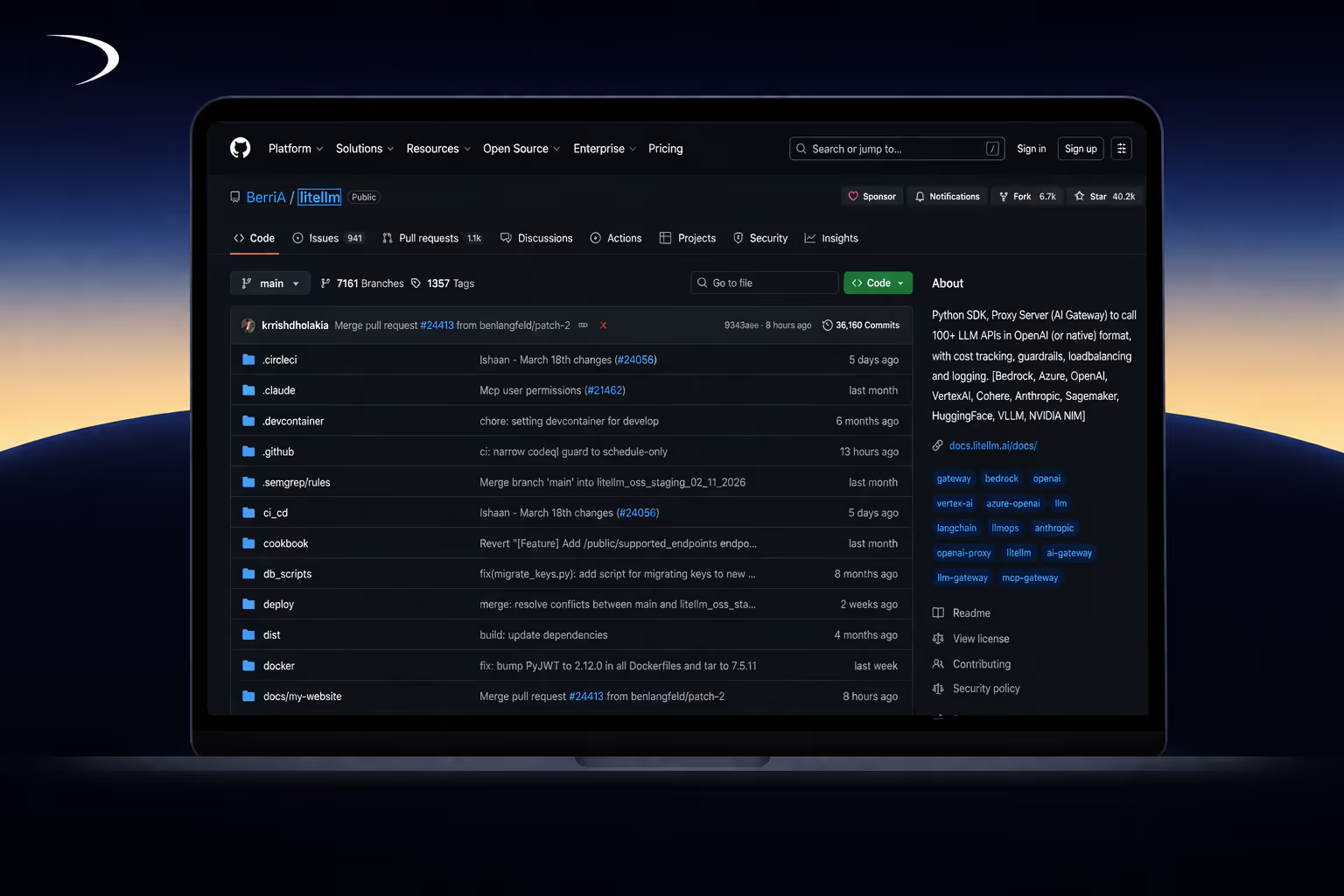
A malicious version of the popular Python library litellm was published to PyPI, exposing developer and production environments to credential theft.
The affected version, litellm==1.82.8, contains a hidden payload that executes automatically on Python startup and attempts to extract sensitive data from the system.
At Daylight, we identified this activity while investigating a high-severity Wiz alert in a customer environment. The alert was“Python script executed base64 encoded code”, which is not highly suspicious on its own, but warranted further investigation.
Shortly after, public reports began to emerge, including a pull request on the litellm repository flagging the compromised version.
What Was Compromised
The malicious release was distributed as part of litellm==1.82.8 and included a file named litellm_init.pth.
In Python, .pth files located in site-packages are automatically executed every time the interpreter starts. This means the payload runs without importing the library, without explicit execution, and without any user interaction beyond installation.
Unlike earlier incidents in this campaign that primarily affected CI/CD pipelines, this mechanism allows execution across developer machines, servers, and production systems.
What the Payload Does
Once triggered, the payload begins systematically collecting credential material from the environment.
It targets cloud and infrastructure access such as AWS credentials, Kubernetes configurations, and cloud provider authentication data. It also gathers developer credentials, including SSH keys, git credentials, and local configuration files.
In addition, it extracts environment variables, API keys, and configuration files commonly used in CI/CD pipelines and application deployments. Other sensitive artifacts — including TLS certificates and even cryptocurrency wallet keys — are also within scope.
This is not targeted access. It is broad credential harvesting designed to maximize exposure in a single execution.
Exfiltration and Persistence
The collected data is encrypted and sent to an external endpoint:
models.litellm[.]cloud
The domain closely resembles legitimate infrastructure, making it difficult to distinguish from expected traffic during routine monitoring.
On non-ephemeral systems, the malware establishes persistence by installing a script (sysmon.py) that periodically polls another domain:
checkmarx[.]zone
This allows the attacker to retrieve additional payloads and maintain access beyond the initial compromise.
A Campaign, Not an Incident
This activity is consistent with a broader supply chain campaign attributed to the group known as TeamPCP.
In the span of a few days, this campaign has moved across multiple layers of the developer ecosystem — from security tools like Trivy, to CI/CD integrations, and now to AI libraries.
The pattern is consistent.
Trusted tools are compromised.
Code executes automatically in high-privilege environments.
Credentials are collected and exfiltrated at scale.
The litellm incident introduces a new delivery mechanism that expands the attack surface beyond pipelines into any system running Python.
Indicators of Compromise
The following indicators are associated with this activity:
- models.litellm[.]cloud
- 46.151.182[.]203
- checkmarx[.]zone
- 83.142.209[.]11
- litellm_init.pth
- sysmon.py
- tpcp.tar.gz
- litellm==1.82.8
- 71e35aef03099cd1f2d6446734273025a163597de93912df321ef118bf135238
These should be correlated with system and network telemetry to identify potential exposure.
What to Do Now
If your environment may be affected, immediate action is required.
Check whether litellm version 1.82.8 is installed and search for the presence of litellm_init.pth. Its existence indicates that the payload has already executed.
Remove the package and any associated files, including sysmon.py, and review your systems for persistence mechanisms.
Most importantly, rotate all credentials that were accessible from affected environments. This includes cloud credentials, API keys, SSH keys, and any secrets exposed through environment variables.
Finally, review recent activity across your infrastructure and ensure that dependencies are pinned to verified versions to prevent similar exposure.
Any system that installed this version should be treated as compromised.
Closing Thoughts
The litellm compromise reflects a broader shift in how supply chain attacks are executed.
Rather than exploiting vulnerabilities in application code, attackers are targeting the tools developers rely on to build and operate systems. These tools run with high levels of trust and often have direct access to sensitive credentials.
As this campaign demonstrates, compromising a single component in the toolchain can expose far more than the application itself.
The attack surface is no longer just the code.
It is the entire development ecosystem.





